SDK-First Integration
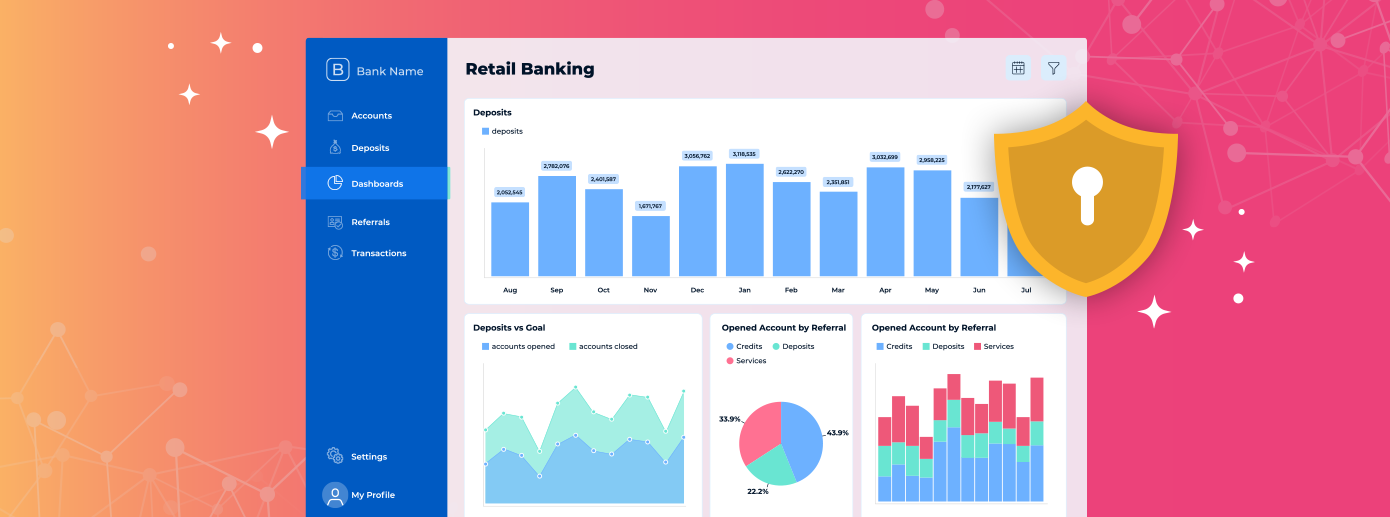
Built to operate within your application's security model and infrastructure.
- Operates within your application's security and deployment model
- Does not own or monetize customer data
- Authentication, authorization, and data access remain under your control
- Deployment flexibility without sacrificing security